M.Tech in Cyber Security
Admission Closed

Program Eligibility
- Applicants must hold a B.E./B.Tech. in Engineering or an MCA/MSc (in Physics, Mathematics Statistics, CS, IT, DS, or related fields) or an equivalent degree.
- A minimum of 60% or a 6.0 CPI on a 10-point scale (or equivalent) in the qualifying degree is required.
- The program is designed for working professionals, and while specific work experience requirements may vary, a background in the IT industry is highly recommended.
- Marks will be relaxed by 2.5% or 0.5 CGPA or CPI against each additional year of experience.
Who is this Program For?

Software Engineers & IT Professionals
Looking to transition into cyber security roles
Network & Infrastructure Engineers
Aiming to build advanced capabilities in secure system architecture
Security Analysts & Practitioners
Seeking to deepen expertise in threat detection and defence
Enterprise Security & Risk Professionals
Managing security, compliance, and organizational risk
Aspiring Cyber Security Specialists
Interested in offensive security, digital forensics, SOC, or threat intelligence
Program Objectives
Secure Infrastructure
Develop advanced expertise in cyber security frameworks required to design resilient digital infrastructure.
Cyber Risk Strategy
Prepare professionals to lead security initiatives by developing effective risk strategies and policies.
Ethics & Compliance
Strengthen understanding of cyber laws, regulatory frameworks, and ethical practices governing security operations.
Total Defense
Build expertise across offensive approaches like penetration testing and defensive practices like SOC operations.
Analytical Investigation
Enhance analytical and investigative capabilities required to assess complex security incidents and malware.
Future Readiness
Nurture an adaptable learning approach to stay ahead of the continuously evolving global threat landscape.
Course Structure
Semester I
| Course Code | Course Name |
|---|---|
| EMCY101 | Foundations of Cyber Security |
| EMCY102 | Computer Networks & Communication Protocols |
| EMCY103 | Network Security & Firewalls |
| EMCY104 | Secure Programming & Code Analysis |
| EMCY105 | Cyber Laws, Ethics & Compliance |
Semester II
| Course Code | Course Name |
|---|---|
| EMCY201 | Applied Cryptography |
| EMCY202 | Operating System & Endpoint Security |
| EMCY203 | Vulnerability Assessment and Penetration Testing (VAPT) |
| EMCY204 | AI & ML for Cyber Security |
| EMCY205 | Data Science for Security Analytics |
Semester III
| Course Code | Course Title |
|---|---|
| EMCY301 | Cloud Security Architecture and Operations |
| EMCY302 | Elective-1 |
| EMCY303 | Elective-2 |
| EMCY304 | Elective-3 |
| EMCY305 | Elective-4 |
Semester IV
| Course Code | Course Title |
|---|---|
| EMCY401 | Elective-5 |
| EMCY402 | Elective-6 |
| EMCY403 | Project Work / Research + Dissertation |
Elective Pool
| Elective Pool - 3 from each pool - Mandatory | ||
|---|---|---|
| Sr no | Offensive Security & Threat Intelligence | Defensive Security & GRC |
| 1 | Malware Analysis & Reverse Engineering | Security Operations Center (SOC) Management |
| 2 | Network Exploitation and Forensics | Threat Hunting & Deception Technologies |
| 3 | Wireless & IOT Security | Cloud Native Security Operations & Resilience |
| 4 | Web and Mobile Application Exploitation | Information Security Risk Management |
| 5 | Advanced Penetration Testing and Exploit Development | Security Auditing & Compliance Frameworks |
| 6 | Digital Forensics & Incident Response | Identity and Access Management (IAM) |
| 7 | Advanced Threat Intelligence and Hunting | Data Loss Prevention (DLP) |
| 8 | Application Security Testing (DAST/SAST) | Third Party RisK Management |
Tools You'll Work With






























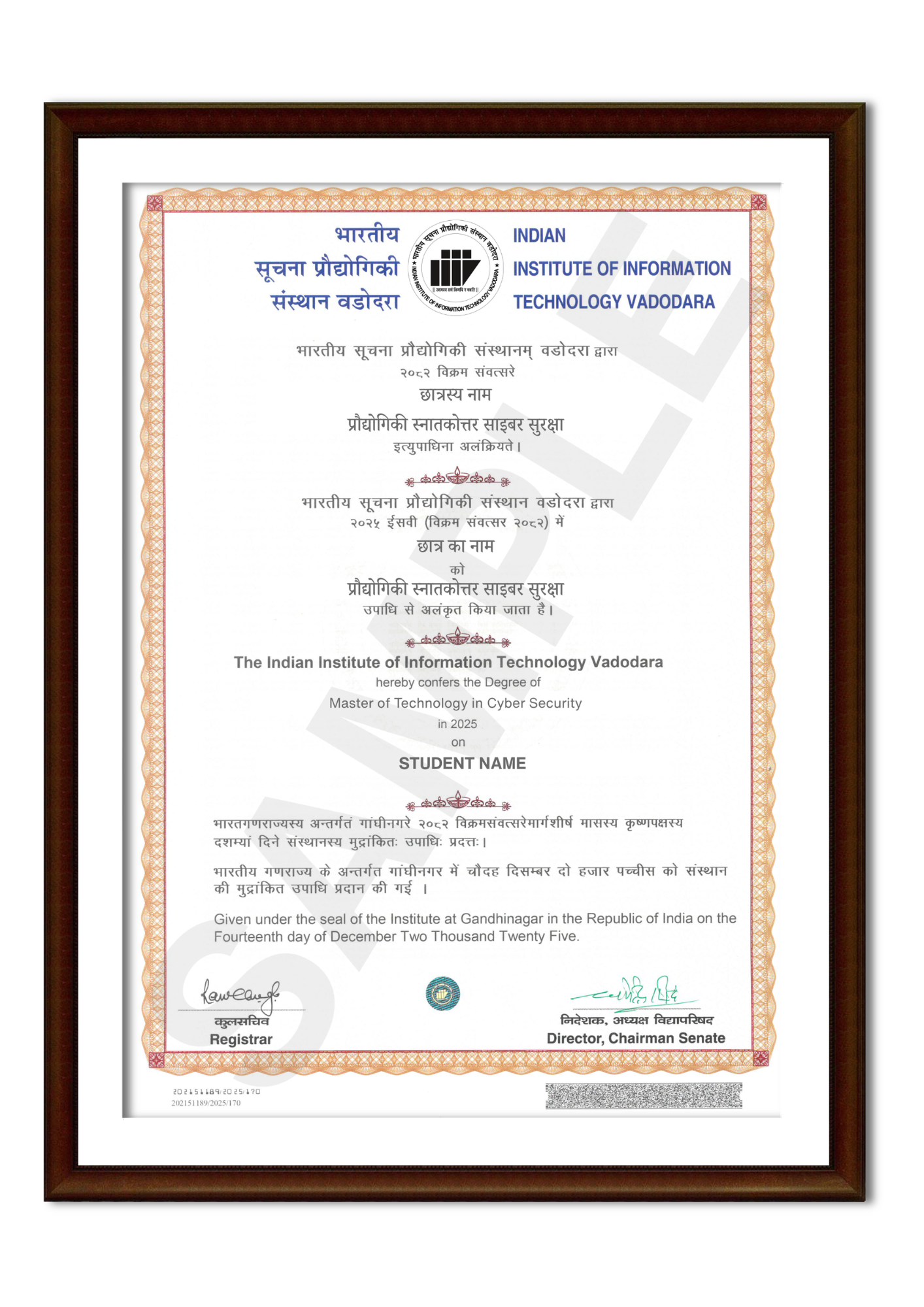
Program Certificate
Skills You Will Gain
Advanced Network Security Practices
Vulnerability Assessment & Penetration Testing
Digital Forensics Investigation Techniques
Threat Intelligence Analysis
Security Operations Centre Management
Applied Cryptography Techniques
Cloud Security Architecture
Malware Analysis Fundamentals
Program Highlights
M.Tech from an Institute of National Importance
Earn a recognised M.Tech degree from IIIT Vadodara, strengthening your academic credentials and long-term professional credibility.
IIIT Vadodara Alumni Status
Become part of the IIIT Vadodara alumni network and strengthen professional connections.
Designed for Working Professionals
The program’s hybrid learning model with live online sessions enables professionals to pursue advanced education while continuing their careers.
Advanced Cyber Security Curriculum
Gain exposure to critical domains such as network security, cryptography, digital forensics, cloud security, penetration testing, and threat intelligence.
Dual Security Specialisation Pathways
Develop expertise across offensive security techniques such as penetration testing and threat hunting, as well as defensive security practices including SOC operations and incident response.
Hands-On Learning with Real Security Challenges
Work on practical assignments, security labs, and a final project or dissertation focused on solving real-world cyber security problems.
Faculty Expertise & Academic Rigour
Learn from experienced IIIT Vadodara faculty and researchers specialising in cyber security, distributed systems, and information security.
Campus Immersion Experience
Participate in on-campus learning sessions designed to enhance peer collaboration, faculty interaction, and practical exposure.
Program Outcomes
-
Secure System Architecture Development
Ability to design and implement secure computing environments using principles of network security, cryptography, and secure system engineering.
-
Vulnerability Assessment & Risk Mitigation
Ability to identify system vulnerabilities, conduct penetration testing, and implement appropriate mitigation strategies.
-
Intelligence-Driven Threat Analysis
Ability to leverage security analytics, machine learning techniques, and threat intelligence to detect and analyse cyber threats.
-
Enterprise Security Management
Ability to secure enterprise IT environments including networks, operating systems, endpoints, and cloud infrastructure.
-
Cyber Incident Investigation & Response
Ability to conduct digital forensic investigations, analyse security breaches, and implement structured incident response mechanisms.
-
Ethical and Regulatory Cyber Practices
Understanding of professional ethics, legal obligations, and regulatory frameworks relevant to cyber security operations and governance.
Alumni Benefits
Alumni Status from IIIT Vadodara
Become part of a growing network of technology professionals and graduates.
Access to a Diverse Professional Network
Connect with alumni across industry, academia, startups, and government sectors.
Collaboration Opportunities
Explore partnerships in industry projects, research initiatives, and consulting engagements.
Peer-to-Peer Learning Ecosystem
Engage with experienced professionals for continuous knowledge exchange and insights.
Lifelong Learning & Upskilling
Stay updated with evolving technologies through ongoing alumni interactions.
Expand Your Professional Circle
Build meaningful connections that support long-term career growth.
Note : Alumni status is granted only to M.Tech graduates
Campus Immersion
Experience a mandatory 5-day on-campus immersion at Indian Institute of Information Technology Vadodara, scheduled in July or December based on your cohort. Hosted at the IIITV-ICD campus in Diu, this immersion is designed to enable in-person learning, peer interaction, and deeper academic engagement.
What’s Included
Hostel accommodation at IIITV-ICD campus, Diu provided on a shared basis.
- In-person academic sessions and peer interactions.
- Opportunity to engage with faculty and fellow participants.
What’s Not Included
- Travel to and from the campus
- Personal expenses during the stay
Fee Structure
| Fees Components | Sem I | Sem II | Sem III | Sem IV | ||||
| Institute Registration Fees | 1,000 | 1,000 | 1,000 | 1,000 | ||||
| Tuition Fee | 85,000 | 85,000 | 85,000 | 85,000 | ||||
| Caution Deposit (Refundable) | 10,000 | - | - | - | ||||
| Academic Charges Inc (Convocation Fee, Alumni Fee, Insurance, ID card Fee) | 3,600 | 2,000 | 3,500 | 2,000 | ||||
| Campus Immersion Fee | 5,000 | - | - | - | ||||
| Total | 1,04,600 | 88,000 | 89,500 | 88,000 | ||||
Note:
|
||||||||
Admission Process

Online Application

Payment of Application Fees
(Non Refundable)

Document Verification

Offer letter issued upon selection

Payment of Admission Fees
Program Coordinator

Prof. -
Associate Professor
Lorem Ipsum is simply dummy text
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry's standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book. It has survived not only five centuries, but also the leap into electronic typesetting, remaining essentially unchanged. It was popularised in the 1960s with the release of Letraset sheets containing Lorem Ipsum passages, and more recently with desktop publishing software like Aldus PageMaker including versions of Lorem Ipsum.Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry's standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book. It has survived not only five centuries, but also the leap into electronic typesetting, remaining essentially unchanged. It was popularised in the 1960s with the release of Letraset sheets containing Lorem Ipsum passages, and more recently with desktop publishing software like Aldus PageMaker including versions of Lorem Ipsum.